Today, the Internet is one of the most progressive inventions, which brings great benefits to all mankind. But from the World Wide Web you can get not only benefit, but also harm. A lot of insidious viruses, spyware, Trojans and other infections are waiting on the "web" that pose a real threat to a desktop computer, laptop, smartphone, OS (operating system). But we must remember that infection also occurs through disks, flash drives, floppy disks, infected software (software).
How to provide reliable protection to ensure the health and safety of your computer?
First of all, you need to remember about antivirus programs that ensure the safety of all your data. To date, antivirus programs. You can download a free antivirus from this site. A reliable program prevents malware from getting into your computer. Well, if a particularly nimble worm, Trojan or spyware still leaks, then the anti-virus software package will immediately begin to work to neutralize them. The effectiveness of the antivirus is very dependent on the regularity of receiving new updates. You need to check once a week. When an “infection” is detected, the antivirus offers reliable options for removing the virus.
The antivirus scanner is used if malware blocks the antivirus or if this package has not been installed. It can only be started by the user. This utility functions in parallel with the action of the antivirus. There is no conflict between them. Most importantly, the scan program will destroy all malware on the computer. But this is a one-time emergency fix. Each time in case of trouble, you need to download the program in a new way (for free).
Firewall (translated as "wall of fire") or firewall, serves to control the situation every minute. The firewall will tell you in time - under what program a Trojan, rootkit or some other rubbish can be hiding. By activating the firewall, you get a smart assistant. A free program can be downloaded to secure your computer in minutes. There are firewalls for advanced users and simple versions. The detector program is designed to send a signal when the device is attacked by third-party viruses. The detector is not installed as often as the above security software.
You can also download free programs that contain many useful features and functions. They include specially designed information products that ensure the security of devices in all directions. They have the additional ability to jointly perform the tasks of an antivirus, antispyware, antitrojan, scanner, firewall, etc.
Software for computer security free download.
Download latest versions security programs on Windows XP, 7, 8, 10.
Computer security. PC and laptop security utilities in Russian.
Program for creating private virtual network(VPN) and protection against viruses and hacker attacks while connected to Wi-Fi. It will be especially useful for users who often access the Internet from a laptop through public access points.

Hotspot Shield for Windows is a ubiquitous program that will certainly be appreciated by those who often work with a laptop in cafes, hotels or shopping centers. When you connect to Wi-Fi, you probably don’t think much about the fact that it’s much easier for hackers or well-written viruses to get access to your data in this way.
version: 10.6.0.1144 from 12 July 2019Powerful free antivirus 360 Total Security with an optimization function works on five engines at once and is able to provide comprehensive real-time protection for all your devices.

Introducing an uncompromising antivirus solution from the Chinese developer Qihoo 360, which will help you reliably protect your computer from viruses, rootkits, trojans and other threats, as well as restore the system, clean it of unwanted elements and optimize your PC.
Comodo Internet Security is a set of free programs for comprehensive protection of your computer from viruses, trojans, ... and attempts to hack your computer from the Internet.

This package includes programs such as:
- Comodo Antivirus - protection against viruses, trojans, worms...;
- Comodo Firewall - protection against hacker attacks via the Internet;
- Comodo Defense+ is an operating system security system.
Russian-language Comodo antivirus is able to protect your computer and prevent the penetration of unwanted programs and virus threats, including those originating from the Internet, while it does not require registration or purchase of a license.
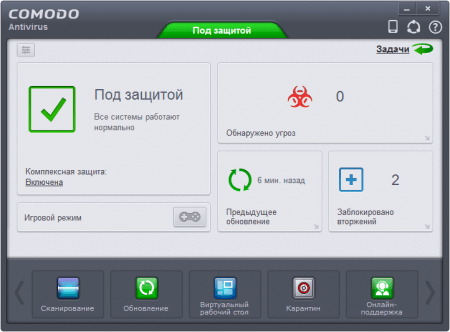
Each computer must be under continuous antivirus protection. But in the era of commerce, it is very difficult to find a really high-quality antivirus that will also turn out to be free. One of the few is Comodo Antivirus.
version: 8.5.4 from 10 July 2019Tor Browser for anonymous web surfing. It is a Firefox web browser with an integrated Torbutton extension, a script blocker and an add-on for logging into sites via HTTPS.

The program allows you to visit sites prohibited by the administrator or the state, as well as to correspond in web chats, place orders and upload files, hiding your IP address and other identification elements.
version: 15.0.1906.1432 from 02 July 2019Free antivirus Avira Free Antivirus 2019 is for non-commercial use. But despite its free status, this program offers a full range of features related to the detection and removal of malicious modules.

The program has a special wizard for more convenient updating of anti-virus databases.
version: 11.1.2 from 01 July 2019Dr.Web CureIt is a free anti-virus tool that provides a quick search for vulnerabilities and neutralizes them when found. The program works without installation and helps restore system performance even in case of serious infections.
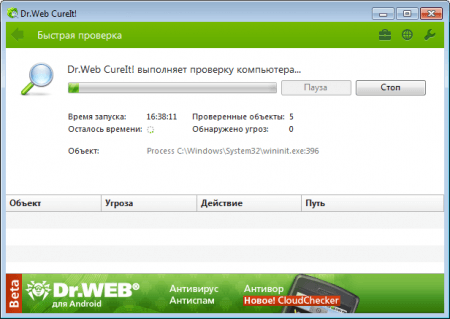
There are times when malicious applications disrupt the computer. The Doctor Web CureIt application is able to revive it in the shortest possible time. It does not require installation, it can detect various types of virus threats, and most importantly, it is absolutely free. You just need to download the latest version of Dr.Web CureIt, start the scan process, after which, if viruses are detected, the program will offer to neutralize them.
version: 15.0.22.0 from 01 July 2019Kaspersky Virus Removal Tool is a utility for detecting and removing viruses from an infected computer.

Internet security is a very important issue of today. And it concerns everyone, from children to pensioners. It is becoming more and more relevant due to the massive arrival of Internet users who are almost, if not completely unprepared for the threats that await them. Therefore, this article will be devoted to such an issue as security on the Internet. After all, not one user suffers, but many others, united in one global structure.
The dangers that lie in wait for us online
In short, there are two main possibilities for how your computer can become a victim. The first is that you yourself, wandering through various sites or installing software from unverified sources, and sometimes from verified ones, infect your computer. Secondly, a situation is also possible when attackers deliberately, using, for example, Trojans or viruses, make your device a source of danger.
As a result of all this, the computer, sometimes even secretly from its owner, starts sending spam, participates in DDoS attacks on various sites, and steals passwords. It also happens that the provider is forced to forcibly disconnect such a device from It turns out that if the user is not aware of what the basics of security on the Internet are, he will have a hard time.
Why do attackers need access to the user's computer
In vain, an ordinary user thinks that no one needs his computer. It used to be that hackers often wrote viruses just for fun, but now it's almost always done for commercial gain. About 20 years ago, an attacker took pleasure in the fact that he could simply format a hard drive. Or make it so that when you turn on the computer, instead of the standard desktop, some cool pictures will appear. Now they are doing everything possible so that the PC owner does not know for as long as possible that his device is infected and secretly performs additional functions.

What is all this for? In addition, as mentioned above, hackers try to gain access to your emails, wallets, accounts in in social networks, forums. It happens, for example, that you go to bed with 20,000 rubles on your electronic wallet, and in the morning you receive an SMS message stating that there is no more money on it. And from the mail all your contacts, and not only, receive spam letters, and even trojans. Hackers can combine many infected computers into a single powerful network, carry out a DDoS attack even on powerful government servers. From the simplest, but also bringing money: they will block the operation of the operating system and demand money for fixing the problem. And, by the way, the money will be taken, but the computer will be left blocked. So security on the Internet should be the basis of your work on it.
How do intruders get into a computer? detailed information
In order to crack the protection of the PC, even if it is, hackers use a number of methods, and users needlessly think that by simply installing an antivirus, they got rid of the danger, for example, to pick up a malicious program. Therefore, before looking for information on how to properly maintain security on the Internet, you need to understand where viruses and trojans come from. Now we will list the main ways of their penetration and methods of stealing various information.

- The first method is called Thanks to various psychological tricks, tricks and gullibility of users, hackers send you a completely harmless file or letter, and you yourself launch a Trojan in it. Or, at the request of the alleged administration of the service, you give out all your passwords and appearances.
- The second method - various free software is offered, pirated disks, where a lot of viruses, trojans and the like are hidden.
- Security holes are constantly appearing in software, including those from the most reliable trusted sources. This also applies to operating systems. Here attackers carefully and monitor such moments, try not to miss them, but use them for their own purposes. You go to some page of a site that has been checked a hundred times and - once - your device is infected.
- The fourth method has received special distribution recently. This is phishing when fake websites are created. And instead of the page of your bank, you find yourself on its fake copy. We won’t talk about what could be next, you can guess for yourself.
Initial protection of the user's computer
Ideally, having bought a PC, the user must perform a number of operations before rushing to surf the endless expanses of the network. We will now present some of the very first Internet security lessons.

Further Safety Lessons
Now a little information on how to ensure the safety of working on the Internet. After completing the previous section, continue to remember to protect yourself daily.

Some more Internet safety lessons
Now let's briefly talk about some more precautions. If you receive a password verification email from your bank, don't hesitate to send it to them. Banks never make such requests. All have a spam filter. Trust him. If you receive a letter about winning a million rubles or an inheritance of five million dollars, delete them immediately. We recommend installing comprehensive protection. It is more reliable than an antivirus from one manufacturer, a firewall from another, and an antispyware program from a third.

Give preference to paid versions. Since Opera and Internet Explorer are the most common browsers, there is more than anything for them and viruses. Use alternatives: Apple Safari, Google Chrome And Mozilla Firefox. Do not use unlicensed software as it may have spyware installed by default. If you shop online, use only trusted options. The same applies to any other online service. Follow all these requirements, and then security on the Internet will be more or less guaranteed.
Children and the Internet
In connection with the development modern technologies More and more children are getting access to the Internet. And if before they mostly played games without even going online, now everything is completely different, and you yourself know everything. Therefore, a new task has appeared - to ensure the safety of children on the Internet. This is quite difficult, since initially it develops completely uncontrollably.

It contains a lot of information that children should not have access to. In addition, they need to be taught how not to "catch" viruses and trojans. Who will help them with this if not adults. In addition, information security on the Internet is very important, since children are completely inexperienced users. They can easily fall for the bait of an experienced scammer or intruder.
How to teach kids how to use the internet
The very first advice is that the child should spend the first sessions on the network with one of the adults. It is advisable to use programs such as to control all the activities of children on the Internet.

It is necessary to limit the independent use of mail and chats, because it can even be dangerous. Since there, for example, pedophiles can look for victims. We will give some recommendations on how you can try to ensure the maximum safety of children on the Internet.

When your child is 14-16 years old, it is unlikely that you will be able to understand computers, the Internet and all such things more than him. Although, of course, one should not forget about control and influence on it. Moreover, it is necessary to remember about such a problem as ensuring security on the Internet. After all, if the computer is shared, or all devices are connected to a single home network, then the threats will be common. In addition, you can always view reports on the activities of the child. It is recommended not to conflict with the child about this, but to try to communicate and find a common language. Despite objections, try to force them to accept the rules for using the Internet, tell them which sites cannot be visited.

A PC with network access must be installed in a common room. This will hold your child back a little. Install software that blocks unwanted sites, do not allow any programs to be installed without your consent. And do not forget to ensure that children do not become addicted to the Internet. We hope that our tips will help protect your computers from threats.
09.11.2005 Jerry Cochran
Free network testing tools - use them before hackers
There are thousands of tools, both commercial and free, for professionals who need to assess network security. The difficulty lies in choosing the right tool for a particular case, which you can trust. To narrow things down, in this article, I'm bringing you 10 excellent free network security analysis tools.
The network security assessment process consists of four main steps: data collection, anchoring, assessment, and penetration. The data collection phase searches for network devices using real-time scanning using the Internet Control Message Protocol (ICMP) or TCP protocols. The Binding and Evaluation phases identify the specific machine on which the service or application is running and evaluate potential vulnerabilities. During the penetration phase, one or more vulnerabilities are exploited for privileged access to the system, followed by privilege escalation on a given computer or across an entire network or domain.
1. Nmap
The time-tested Network Mapper (Nmap) tool has been around for several years and is constantly being improved by the author. Nmap is an indispensable tool for a network security specialist, the value of which cannot be overestimated. Nmap can be used in various ways in the data collection phase for real-time scanning to identify systems active on a given network. Nmap is also useful for discovering a router's ACL (Access Control List) or firewall rules by checking the acknowledgment flag (ACK) and other methods.
During the binding and evaluation steps, Nmap can be used to scan ports, enumerate services and their version numbers, and collect distinguishing information about operating systems. Nmap is an excellent tool for in-depth analysis and verification of results automated program scanning. Nmap was originally designed for UNIX, but has been ported to the Windows platform in recent years. Nmap is an open source program and can be downloaded for free from several sites, the main one being - http://www.insecure.org/nmap .
2.N-Stealth
One of the most difficult steps in the analysis of violations in the security system is the assessment stage. Identifying active systems and the services that run on them is easy, but how do you figure out how vulnerable a particular service is? An effective Web services tool is N-Stalker's N-Stealth Security Scanner. The company sells a more fully featured version of N-Stealth, but the free trial is fine for a simple evaluation. The paid product has more than 30,000 Web server security tests, but also free version finds over 16,000 specific gaps, including vulnerabilities in widely used Web servers such as Microsoft IIS and Apache. For example, N-Stealth looks for vulnerable Common Gateway Interface (CGI) and Hypertext Preprocessor (PHP) scripts, exploits SQL Server penetration attacks, generic cross-site scripting, and other gaps in popular Web servers.
N-Stealth supports both HTTP and HTTP Secure (HTTPS - using SSL), maps vulnerabilities to the Common Vulnerabilities and Exposures (CVE) dictionary and Bugtraq database, and generates good reports. I use N-Stealth to find the most common vulnerabilities in Web servers and identify the most likely attack vectors. For more information on N-Stealth, please visit http://www.nstalker.com/eng/products/nstealth. Of course, for a more reliable assessment of the security of a Web site or applications, it is recommended to purchase a paid version or a product such as WebInspect from SPI Dynamics.
3.SNMPWalk
SNMP is a well-known, widely used, and completely insecure protocol that operates over UDP port 161. Cisco Systems routers and Windows servers are generally SNMP-compliant and are at best minimally protected by the requirement to specify a pure text string with the community name (community string), to get write and read permissions. To assess the security measures, however weak, SNMP on a network, a tool such as SNMPWalk is useful, with which you can obtain important information from network devices. A simple SNMP query will help detect information leaks from SNMP devices. For example, the well-known standard community string for Cisco routers- ILMI. Using this string, SNMPWalk can extract a wealth of information from Cisco routers that allows you to take full control of the network router infrastructure if a particular important piece of data is stored in the Cisco Management Information Base (MIB).
SNMPWalk is an open source tool that was developed by the Net-SNMP project at Carnegie Mellon University in the early 1990s when SNMP was being introduced. The get-next request is used to retrieve control parameters (in Abstract Syntax Notation, ASN) from the SNMP MIB subtree. As noted, in order to get the right to read information from the device, only a string that is well known or can be easily found on the network is enough. UNIX and Windows versions of SNMPWalk are available at .
4. Pipe
One of the most difficult security tests that is useful to perform on a network is to simulate an intruder attack by looking for ways to bypass one or more lines of defense. An example of a workaround in the scoring or intrusion phases is relaying or port forwarding, and Foundstone's Fpipe tool (a division of McAfee) is perfect for this. To bypass router access control lists (ACLs), firewall rules, and other security mechanisms, it is sometimes possible to access a specific service running on a port by redirecting or tunneling traffic to the desired TCP port through a different TCP port.
A simplified example is a subnet router that only allows HTTP traffic on TCP port 80. Suppose you want to connect to a Telnet machine (TCP port 23) on a different subnet. If you manage to infiltrate another system on the same subnet as the Telnet machine, you can use a port relay such as Fpipe to set up a TCP or UDP "flow" that encapsulates traffic for TCP port 23 in packets identified as TCP port 80 packets. These packets pass through a router that allows TCP port 80 traffic and arrive at the affected computer running Fpipe or another port relay. This port relay "stripped" packets and forwarded TCP port 23 traffic to the intended recipient.
You can also use Secure Shell (SSH) or Netcat (described below) for port forwarding and forwarding, but the free, easy-to-use, and well-documented Fpipe program is preferable. latest version Fpipe can be obtained from http://www.foundstone.com .
5.SQLRECON
Over the past few years, many vulnerabilities have been identified in SQL products such as Microsoft SQL Server, Oracle Database, and Oracle Application Server. The most notorious threat was the SQL Slammer worm in 2003 (description published at http://www.cert.org/advisories/CA-2003-04.html). Until recently, there was no tool to accurately locate SQL Server instances and their version numbers, so identifying potential flaws in SQL Server systems was difficult. Too often, the tools incorrectly determined the SQL Server version because they pulled information from ports (for example, TCP port 1433, UDP port 1434) that contained the wrong version of SQL Server.
The SQLRECON utility has recently been released and can be downloaded from the Special Ops Security website at http://specialopssecurity.com/labs/sqlrecon. SQLRECON scans the network or host machine, identifying all instances of SQL Server and the Microsoft SQL Server Desktop Engine (MSDE). The main advantage of the tool is that several well-known SQL Server/MSDE binding and discovery methods are combined in one utility. Once you have reliable information about the SQL servers (and their versions) on your network, you can start looking for potential vulnerabilities. SQLRECON is not a vulnerability scanner, but rather a discovery tool that greatly simplifies the task of evaluating network security. Now we need a tool for Oracle...
6.Enum
It is useful for a Windows specialist familiar with Linux to have a comprehensive (and free) tool for collecting a wide variety of information about Windows system. Enum is such a tool. Launched from command line the utility with the management console reports the mass useful information about a Win32 computer through a NetBIOS service that runs on TCP port 139. In both null sessions and authenticated sessions, Enum can retrieve lists of users, systems, shares, groups and their members, passwords, and LSA policy information (Local Security Authority - local security manager). Enum can be used to perform primitive dictionary brute-force attacks on individual local accounts. Figure 1 shows detailed information about the Windows system that can be collected remotely using this tool. Enum (along with some other excellent tools like Pwdump2 and LSAdump2) can be downloaded from the BindView site at http://www.bindview.com/services/razor/utilities .
7. PsTools
Most administrators are familiar with Sysinternals' many tools and resources. The PsTools complex is very useful for assessing security. The name of the complex comes from ps (process listing), a command line utility for UNIX. PsTools is a set of tools that fill in the gaps in the usual command-line tools and resource kits for Windows. PsTools is especially useful for assessing security and infiltration of both remote and local computers.
Having penetrated through the loophole, it is very convenient to use PsTools to remotely manipulate the system and expand the attack, in particular, increase the level of your powers. For example, if you managed to sneak into the system and gain local administrative access, but need to elevate to the domain administrator level that is currently logged on, you can use PsTools to perform operations such as remote session termination and process kill.
PsExec is one of the best utilities in the PsTools suite. Thanks to it, a user with local administrative access (via an authenticated network connection) can remotely run programs on the system. A very effective technique is to use PsExec to run cmd.exe on a remote system, which gives you access to a remote command line with administrative privileges (PsExec does not provide such privileges, they must be acquired in some other way). More information about PsExec can be found in an article published in Windows IT Pro/RE #6, 2004.
Other useful programs- PsList to list all processes active on the remote system, and PsKill to kill individual processes on the remote computer. For more information on these utilities, see Windows IT Pro/RE #7, 2004. In addition to evaluating security, PsTools is very useful and easy to remotely perform many administrative operations from the command line (this was probably the main intention authors). PsTools (along with many other resources) can be obtained from the Sysinternals Web site at http://www.sysinternals.com/utilities.html .
8.Netcat
Netcat is widely known as a tool to open backdoors for an attacker to gain access to a system (penetration stage), but less well-known is its ability as a tool for binding and evaluating, as well as performing other important operations that make up the traditional network security evaluation procedure. It was developed over a decade ago for UNIX and ported to Windows in 1998. Netcat is an extension of the UNIX command
with which you can stream the contents of files to and from the screen to view, modify or merge data. With Netcat, you can read and write data from a computer's standard I/O devices over a TCP/IP network. As a result, the user can work with the TCP/IP protocol suite and read/write data through TCP and UDP ports.
In addition to organizing loopholes, Netcat can be used to capture headers (Telnet, SMTP and FTP), file and data pipelining, port scanning, remote binding of services to ports, and many other tasks. Every now and then someone shows me new, previously unknown ways to use Netcat. Most often, I use this utility to connect to a TCP port to try to extract some information from it, and send back a command line prompt from the target system.
The Windows version of Netcat can be downloaded from http://www.vulnwatch.org/netcat. An extremely detailed description of the tool is published at http://www.vulnwatch.org/netcat/readme.html .
9 John the Ripper
Most administrators have probably heard of the L0phtCrack password cracking and auditing tool, originally developed by The Cult of the Dead cow; currently owned and developed by @stake, recently acquired by Symantec. I prefer John the Ripper, a simple, effective password cracker available on many platforms (including Windows), based on the well-known UNIX Crack tool. With John, you can identify system characteristics and capabilities to optimize performance. In my experience, John makes significantly more attempts per second than other password crackers, including L0phtCrack (LC5, the current version of L0phtCrack, is said to be significantly faster than past versions, but comes at a cost).
In addition, John not only exposes hashed Windows passwords (LAN Manager and NT LAN Manager, NTLM), but also cracks any passwords that use ciphertext or DES (standard, single, extended), MD5, Blowfish, or Andrew File System (AFS). John combined with a dictionary file (there are many such files covering almost every known language in the galaxy - even Wookiee and Klingon) is an indispensable tool for password cracking and auditing (a must for every company, no matter how strict its policy). The John the Ripper utility can be obtained from http://www.openwall.com/john or http://www.securiteam.com/tools/3X5QLPPNFE.html .
10. Metasploit Framework
An easy-to-use infiltration platform containing the latest threats, enhanced with features automatic update and extensible with a well-known language such as Perl. However, it is not safe (and rather irresponsible) to provide such opportunities for free to just anyone - it's just a gift for novice hackers (it's like putting a nuclear briefcase on eBay). However, one cannot but admit that a tool such as the Metasploit Framework will be very useful for network security specialists to emulate threats.
The Metasploit Framework emerged about two years ago as the result of a research project led by renowned security expert H. D. Moore. The goals of the project were somewhat noble: to deepen security research and provide a resource for penetration developers. I'm using the Metasploit Framework (with some care and pre-testing in a lab) as a security penetration tool.
Metasploit is a Perl scripting engine that can be used to apply a variety of penetration methods for various platforms and applications (at the time of writing this article, more than 75 penetration methods are known, carrying 75 payloads, and this number is increasing). In addition to a set of methods for penetrating known loopholes, Metasploit allows you to send a specific program to the detected loophole. For example, by infiltrating a system that is not protected from SQL Slammer (see the SQLRECON section above), you can choose how to manipulate the affected system: create a connection using the Win32 Bind shell, send back with the Win32 Reverse shell, simply execute a remote command, inject a harmful server DLL utility Virtual Network Computing (VNC) into the affected active process, or use another method. The Metasploit Framework is extensible with Perl modules, so you can prepare your own penetration tools, include them in your infrastructure, and use a ready-made, suitable exploit. Figure 2 shows Metasploit's easy-to-use Web interface with a list of penetration methods.
 |
| Figure 2: The Metasploit Framework Web Interface |
I recommend that you treat the Metasploit Framework with caution and only use it to demonstrate specific vulnerabilities in your network security analysis. You can download the Metasploit Framework at http://www.metasploit.com .
Safety is a shared concern

It's not enough to just buy a firewall, monitor the network, or scour the Internet for news about the latest threats to protect your network. Each company's IT department and the rest of its employees play an equally important role in ensuring security, according to Lloyd Hession, director of IT security at BT Radianz. He saw this through his own experience. For five years, Lloyd was responsible for the information security of the company, which provides network connections for financial service providers worldwide with leading financial companies. As Director of IT Security, Lloyd ensures that the network is up and running 24/7. Windows IT Pro Senior Editor Ann Grubb recently spoke with Lloyd about how technology, IT and users are helping him secure the BT Radianz network.
What security issues does BT Radianz face?
Radianz connects the world's exchanges, financial information providers and financial transaction services with the world's largest financial companies. In essence, this is a large corporate IP network. The value of transactions made on the BT Radianz network in two or three days can reach the value of the US gross national product: from 11 to 12 trillion. dollars. At the same time, safety is an absolute priority. My primary concern is issues such as fault tolerance, denial of service (DoS) attacks, worms, and viruses that can cause performance degradation.
Do you have a plan that outlines your overall security strategy and how to delegate IT security responsibilities?
We have an internal Security Posture and Framework that we're working on with some of our clients. It describes what the secure network architecture should be, the workflows and disciplinary measures that ensure the ongoing security of the network, the organizational structure, how to respond to incidents, and how to deal with customers in the event of an incident. I'm used to being constantly under close supervision and explaining our security strategy; after all, if you want trust from exchanges and financial firms, they need to be vigilant. I reassure them that we have chosen the best technologies and information services that immediately inform us of vulnerabilities. I have to demonstrate - almost daily - the most serious attitude to safety.
What is the number of employees who ensure network security? What are their responsibilities?
One of the most effective ways to ensure security is to include its requirements in job descriptions, even for those employees who are not security specialists. For example, we have many employees serving the network. It is essential that they are aware of their security responsibilities. The router administrator must understand that many procedures are introduced precisely because of security problems.
So when I'm asked to quickly name the exact number of people responsible for information security, I usually answer: "41". This number includes individuals who have the word “security” in their job titles or who have security as a significant part of their responsibilities. Although, of course, in doing so, I underestimate the contribution of hundreds of network operations center specialists who respond to danger warnings on screens and must bring these warnings to a smaller group of technical specialists. I would call this approach a distributed security system and I believe that as a result, the effectiveness of protection increases.
Do you think that even small organizations with more limited IT resources than Radianz can take this horizontal approach to security management?
You have raised a very important issue. Unlike BT Radianz, most companies cannot afford to have a centralized security department. Therefore, to ensure the effectiveness of protection measures, it may be necessary to appoint a special employee who should direct the work in the field of security and coordinate the actions of system administrators, network engineers, and simply technically literate people. I'm sure it's better to hire someone who understands enterprise technology, with experience in system administration or network maintenance, and train them in information security techniques than to hire a security professional who is excellent in this area but doesn't know the specifics of the enterprise.
What tools and products do you use to secure your network?
We use a number of tools that are not usually classified as security tools, but that provide many benefits nonetheless. We have to manage 40 thousand routers, this cannot be done manually. If employees are allowed to individually configure and manage routers, then the probability of errors will be too high. We can't say sorry, trading on the exchange is canceled today due to a problem with the routers. Therefore, we have a special internal expert system, which, in essence, is a huge database of all possible router configurations. If I suspect that the router has been tampered with, I can compare its configuration with known settings in the database and determine if the changes were made manually, i.e. not by an expert system.
We also use systems management tools commonly used by large network organizations such as telecom operators. The internal network uses layer 2 and layer 3 firewalls; devices for prevention (Intrusion Prevention System, IPS) and detection of unauthorized access (Intrusion Detection System, IDS); proxy servers; spam filters, Email and spyware. However, many of these tools cannot be applied to the production network that we provide to customers.
We also use Symantec's DeepSight Threat Management System on our production network. DeepSight continuously monitors the Internet for security issues, attacks, and successful hacks and alerts us to these threats. DeepSight also advises what needs to be done to eliminate a particular threat. For example, we received advice on how to deal with the SQL Slammer worm and workarounds (blocking traffic on port 1434, the SQL Server port) until Microsoft releases a fix. Thus, using the tool, you can quickly collect the necessary information and decide on the measures that are appropriate in a particular enterprise.
Before we started using DeepSight, two or three experts were constantly up to date with the latest threats - they read bulletins sent by mail, attended conferences and prioritized various alerts. The rationale behind Symantec's Security Focus service, which later became Symantec's property, was the desire to use the company's employees to solve real problems, rather than research work, the results of which are more easily purchased from an independent organization.
How are end users within the company involved in implementing the IT security plan?
If you have only one dollar to spend on security, then spend it on user education. For the main potential danger comes from the reckless actions of employees within the enterprise - downloading programs that they should not download, launching a file in which the "Trojan horse" is hidden. Therefore, any measures that help them recognize the danger will improve feedback to employees and help to avoid many troubles in the future.
In addition, monitoring at the user level is most effective if they report any suspicious events. Each employee must play the role of an individual intrusion detection system. In essence, it is necessary to make people aware of their responsibility for security. We have a list of 14 critical safety principles that every employee should know.
And principle number one is that all employees are responsible for safety. Everyone has a duty - to lock the doors behind them, not to let strangers into the building, not to leave confidential documents on the table, to store laptops securely.
What is the top security threat that IT professionals need to combat today?
Mostly spyware. Most organizations take antivirus hosting very seriously. But not everyone has reliable tools to deal with spyware. Many of my small business contacts complain that spyware is almost shutting down their businesses. Cleaning up systems and restoring performance can be very costly.
